Sending passwords (securely)

As a WordPress development & support company, we tend to have access to lots of client’s website credentials, and we often need to send passwords to clients. In this article, we’ll explore how we do that as securely as possible.
First, let’s look at how not to do it…
Plain Text
When providing someone with credentials to a website (credentials being the username/password combination), you may first reach for the obvious tool: email.
The problem with email is this: email accounts are prone to be hacked, and if they are hacked, all emails are typically stored in plain text – giving hackers a massive database of opportunities.
Breaking up (is hard to do)
One method to improve on this is to break up the credentials into two separate emails; password in one email, username in the other. For the same reason above, this doesn’t add much more protection.
Crossing the Streams
A further extension to the above is to send the password via a different channel like WhatsApp, text, message, or Facebook Messenger etc. These are certainly better than email, though this method is not foolproof.
Tip: if you do this, the best method is to warn the recipient that you are sending the details via email, and then send the password (and only the password) in the other channel (e.g. WhatsApp). That way your WhatsApp message has no context as to what the password means or gives access to.
Alternative: One Time Secret
A better method still is this: grant the recipient one time access to the password information using a system like One Time Secret:
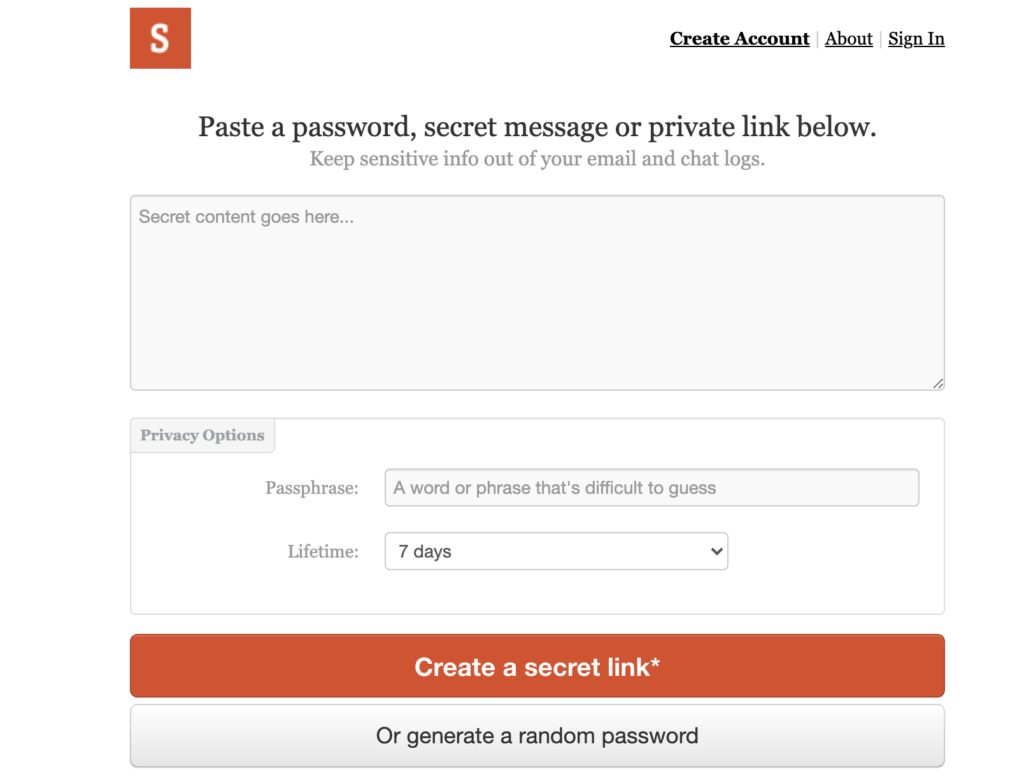
Fig 1 – https://onetimesecret.com/
In Fig 1 above, we see how the main screen of One Time Secret looks.
It’s pretty simple to operate, you:
- Put your secret content (e.g. password) where it says “Secret content goes here….“
- Optionally set a Passphrase (we’ll ignore that, feel free to explore though).
- Optionally change the Lifetime (more on that later).
After that, you just need to click the big ‘Create a secret link‘ button and you’ll see taken to a screen similar to the following:
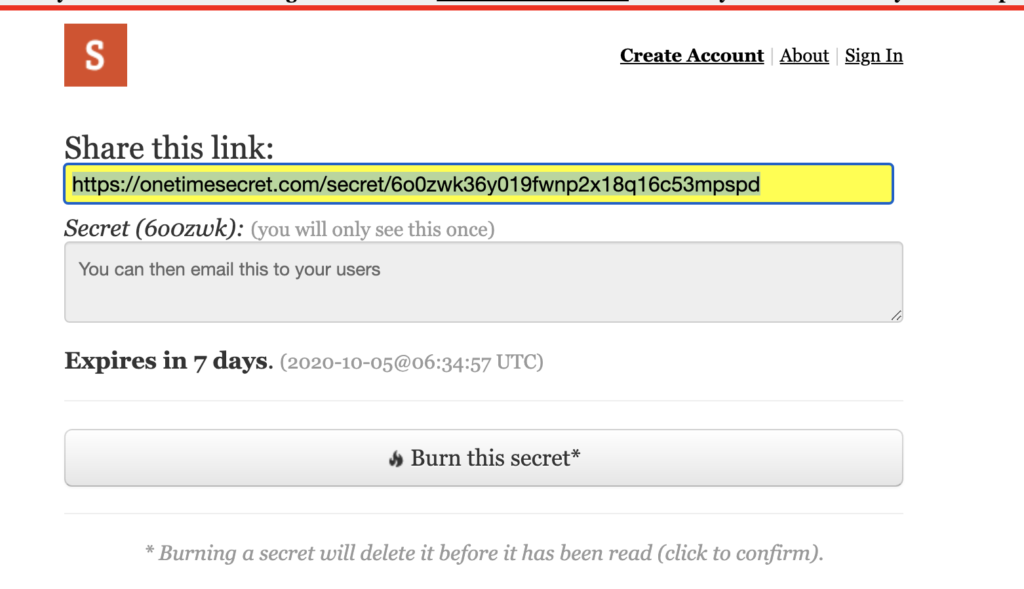
Fig 2 – One Time Secret link
In the screen above, we see that One Time Secret have generated a secret link for you. As you can see, that link is pretty random in nature and is not easily guessable.
You can now send this link (shown highlighted in Fig 2) to your recipient in whatever fashion you like.
The recipient can then click the link, whereby they will see this:
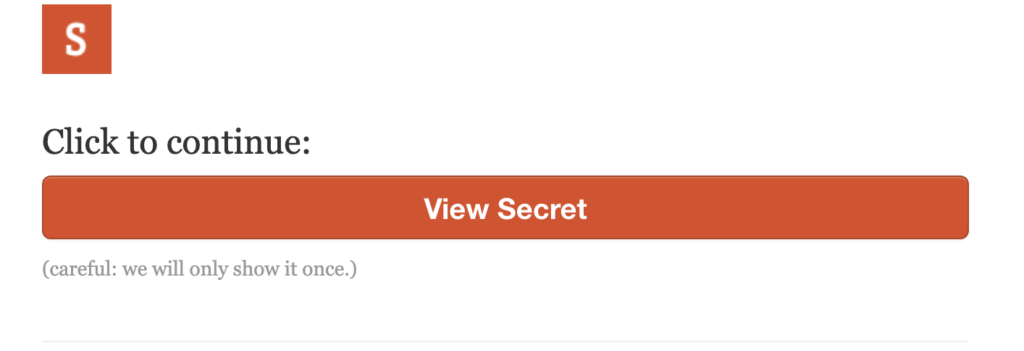
Fig 3 – revealing the secret (step 1)
I shall say zis only once!
Note in Fig 3 that the screen is warning the user that they will show the secret only once!
This ‘only once’ aspect greatly increases the security of the sequence: as soon as the link has been clicked once, it is then deleted and can no longer reveal your secret.
So there is no issue here with hackers stumbling across the link in a hacked email account at some point in the future – as the link should have already been used up.
Note: the eagle-eyed, conspiracy theorists amongst you may well a) be wearing a tin foil hat, and b) already be concocting scenarios where hackers can still circumvent security, and I would agree, no system is infallible. When we are using something like One Time Secret, we typically establish that the client is sat there waiting for the password – which means we can reduce the Lifetime value (see Fig 1) down to (say) 30 mins. We may well even send the link via WhatsApp or similar. This again narrows the window of opportunity for miscreants to misbehave.
Final Thoughts
One Time Secret is not the only system, of course, I have also heard mention of Privnote and Ephemera, (I’ve not used either but, at first glance, they look very similar).
You may think “oh, but what if hackers are actually in charge of One Time Secret etc or hack it?‘ – which is a valid point, but if the information you put into One Time Secret is only the password and without any context (i.e. without surrounding text say ‘This is the login to your website, the URL is……“) then any miscreant would have a pretty hard time making use of your information.
If you have any comments or suggestions here, feel free to join our free Facebook Group where we chat about topics like this, and also run regular events relating to WordPress and websites.
Tags: passwords, security
No Comments
